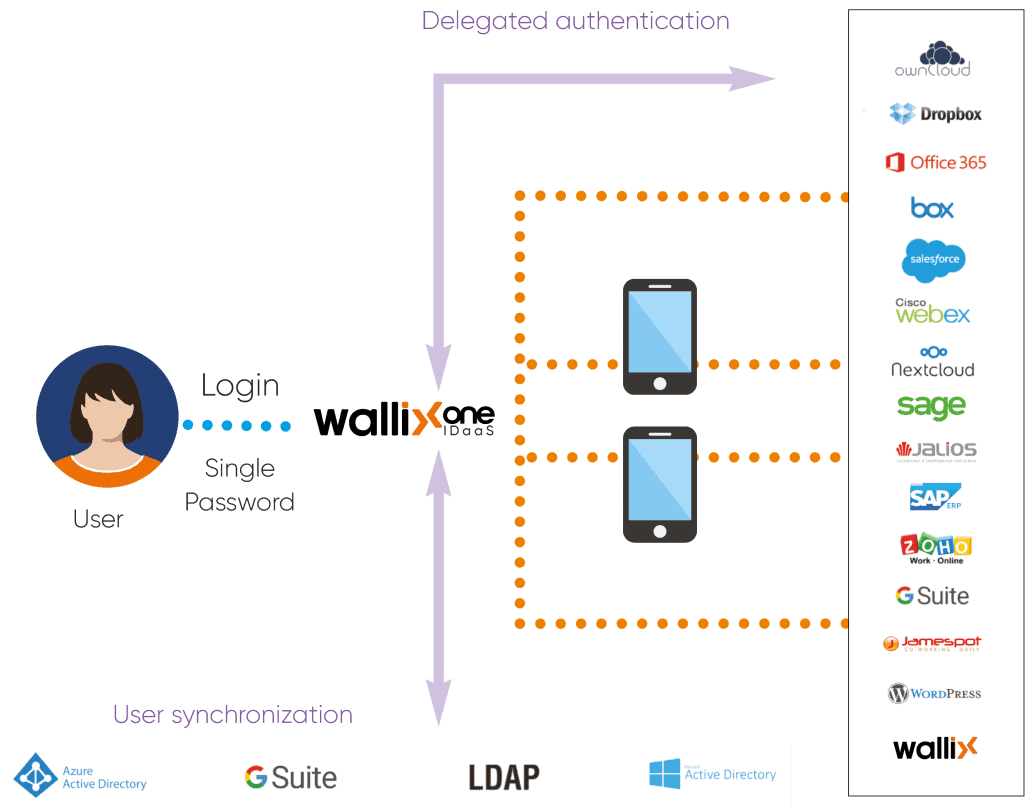
WALLIX One IDaaS
Streamline access, fortify security, and elevate user experience across in-house or cloud applications. Our solution minimizes the risk of breach by integrating a Zero Trust framework, along with Single-Sign-On (SSO) and Multi-Factor Authentication (MFA).